Critical Infrastructure (KRITIS) umbrella law 2026: What operators need to know now
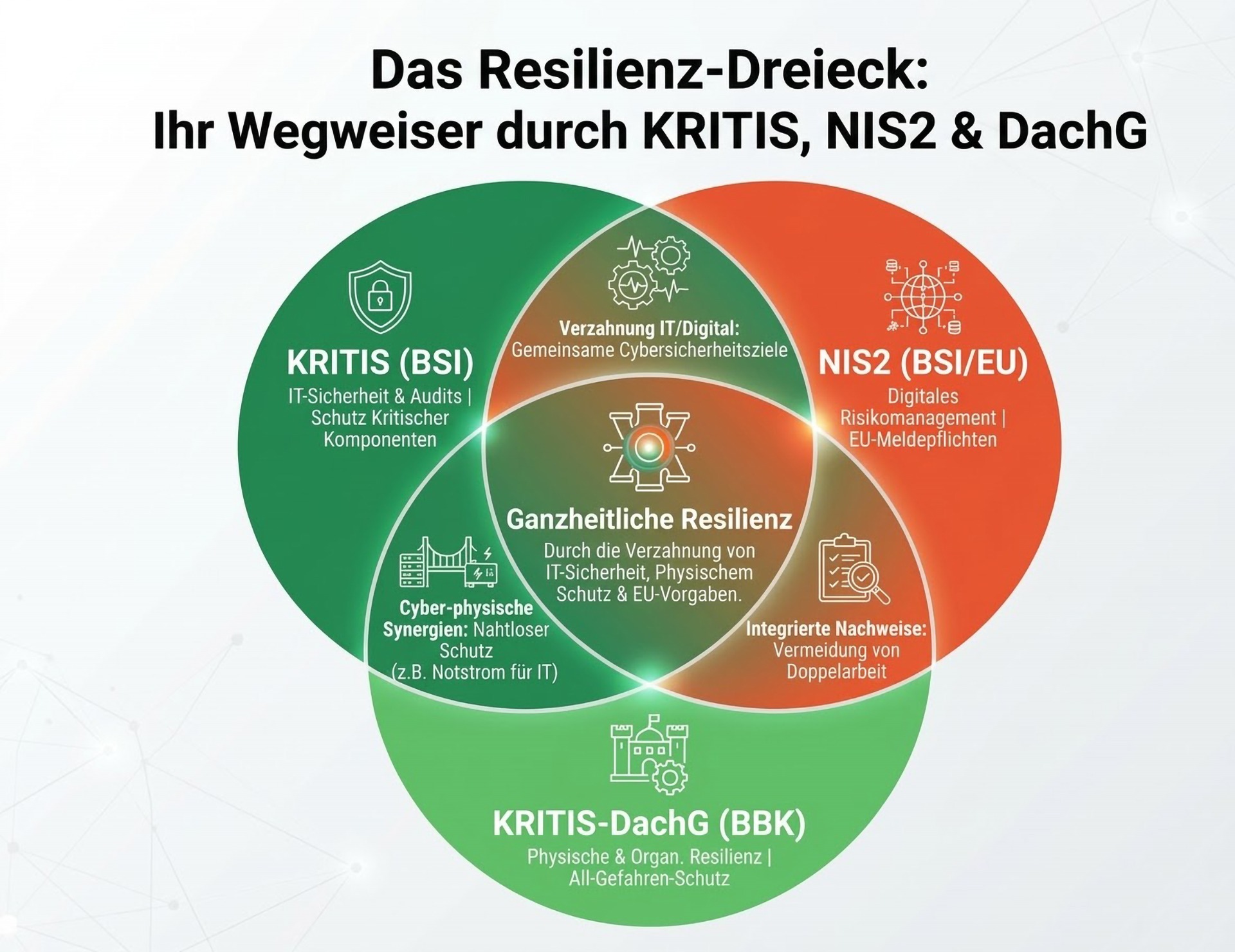
The KRITIS umbrella law (KRITIS-DachG) was passed by the German Bundestag on January 29, 2026, and transposes the EU CER Directive (EU) 2022/2557 on the physical resilience of critical facilities into German law. In terms of content, it is clearly distinct from the "classic" KRITIS requirements for IT security (BSI Act/KRITIS Regulation): The umbrella law primarily addresses physical threats, operational and organizational resilience, not pure cybersecurity.
At the same time, there is a risk of confusion: in practice, operators will have to neatly interlink two strands of regulation in the future (physical/organizational vs. cyber/IT). This article provides an overview, highlights typical obligations, and outlines concrete next steps.
Risk of confusion: umbrella law versus old KRITIS Regulation
The previous KRITIS regulation in the context of the BSI Act focused on IT/cybersecurity and worked heavily with sectoral thresholds. The KRITIS umbrella law broadens the focus to include physical protection and follows an all-hazards approach (e.g., natural hazards, sabotage, terrorism, accidents) – with the aim of preventing and mitigating failures of critical services and accelerating recovery.
Important: The umbrella law does not replace the previous IT KRITIS requirements, but supplements them. Anyone already planning KRITIS/NIS2 obligations should therefore pay particular attention to interfaces and duplication of work.
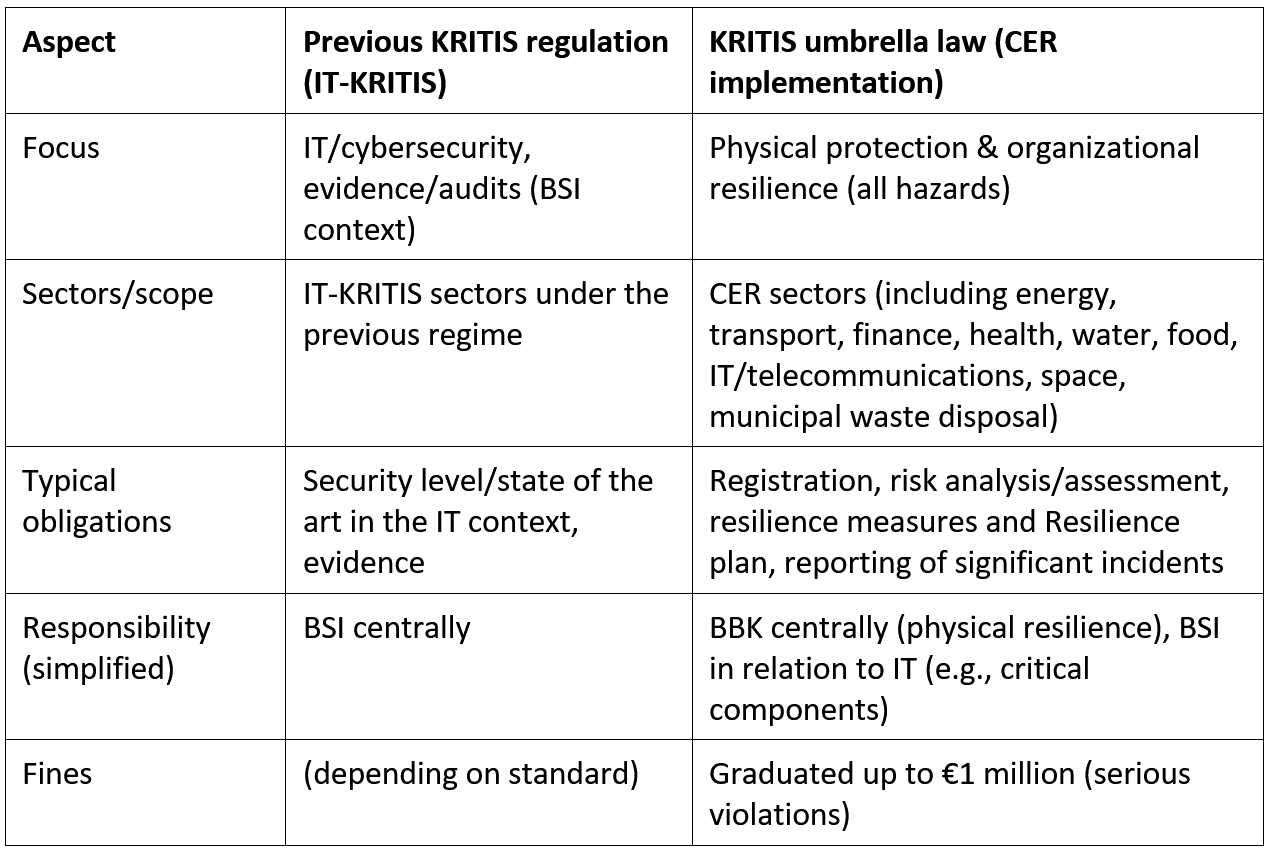
Who is affected and what are the new obligations?
Operators of critical facilities in the sectors covered by the law are affected; as a rule of thumb, it is often said that operators who supply more than 500,000 inhabitants or whose failure would have a significant impact typically fall within the scope of application (a case-by-case assessment remains necessary). Another practical consideration is that federal states may also identify regionally significant facilities as critical even if they fall below the federal thresholds.
New obligations:
- Registration/identification as the basis for subsequent obligations.
- Regular risk analysis/assessment (at least every 4 years).
- Implementation of proportionate resilience measures (e.g., emergency preparedness, property protection, access controls, detection/monitoring, crisis and alarm procedures, emergency power/redundancies, training/drills).
- Written resilience plan (documentation and control center for evidence).
- Reporting system for significant incidents with a deadline of "within 24 hours" for the initial report; follow-up reports/updates are standard (details depend on final specifications/guidelines).
Note on deadlines: In many presentations, "3/9/10 months" are given as guidelines from registration; it is crucial that implementation work should not only start "after announcement" because impact assessment, scope, data collection, and governance take time.
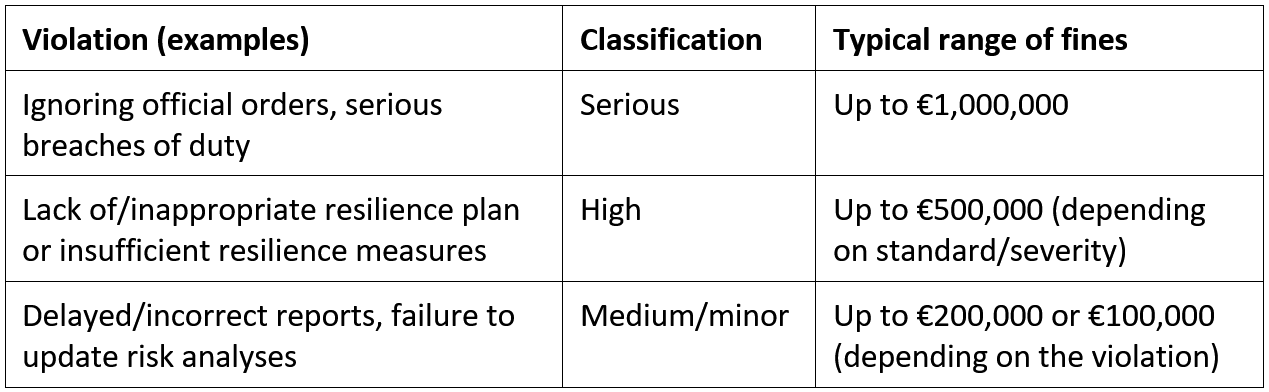
What are the potential fines?
The penalty regulations were visibly tightened in the parliamentary process: in serious cases, fines of up to €1 million are possible. In addition, there are further levels (e.g., €500,000 / €200,000 / €100,000) depending on the type and severity of the violation. In addition to fines, there are other risks: official orders, possible operational restrictions, and liability/reputation risks (especially in cases of ignored cooperation with authorities or failure to report).
Recommendations for operators
- Clarify impact (scope first): Check sector/facility, supply impact, regional significance. In borderline cases, legal clarification is recommended. Also consider the possibility of country identification.
- Leverage synergies with standards: ISO 22301 (BCM) is suitable as a framework for emergency/recovery; ISO/IEC 27001 remains central to cyber/NIS2, but does not fully cover physical resilience (supplementation required).
- Set up a program structure: Project team (compliance/legal, IT security, BCM, property protection/facilities, operations, communication/PR). Clear ownership and escalation paths.
- Create a data and evidence base: Asset/location overview, dependencies (power, telecommunications, supply chains), critical components/IT reference, existing emergency/crisis plans, existing contracts/SLAs.
- Integrate risk analysis & resilience measures: Conduct an integrated assessment (cyber-physical) to ensure that hybrid scenarios do not fall "between two stools."
- Use the resilience plan as a control artifact: Do not treat it as a paper exercise, but as a document that prioritizes measures, responsibilities, tests/exercises, and recovery.
- Prepare reporting & external communication: Reporting processes (24 hours), templates, responsibilities, secure communication channels. At the same time, check the website/press releases to see if they disclose sensitive security details (politically explicitly addressed).
What is the relationship to NIS2 implementation and DIN/ISO 27001?
The KRITIS-DachG should be understood as a supplement to NIS2 and the IT security obligations in the BSI environment: NIS2 primarily addresses cybersecurity, while the umbrella law primarily addresses physical resilience. In highly networked infrastructures, however, both levels overlap (e.g., emergency power/redundancies, access and perimeter protection, operational processes, dependencies, and hybrid cyber-physical scenarios).
Attempts were made to avoid double regulation with NIS2. This was only partially successful.
The risk: duplication of work in analyses, evidence, and reporting, especially when organizations implement cyber and physical resilience in separate silos.
The opportunity: an integrated governance and verification system that consistently combines both perspectives (cyber and physical/organizational), thereby reducing friction losses. Unfortunately, as of February 2026, this issue has not been resolved.
NIS2 focuses on digital risk management and reporting processes for essential/important institutions, while the KRITIS-DachG prioritizes resilience against all-hazard situations (e.g., sabotage, natural disasters, accidents) and provides for its own supervisory and cooperation structure for this purpose (in the DachG context with the BBK as the central authority and interfaces to the BSI in relation to IT).
In practice, coordinated registration and reporting processes between the responsible authorities are provided for, but "holistic" integration is not automatically guaranteed. This can lead to parallel evidence (cyber vs. physical/organizational) and parallel reporting procedures with very short initial deadlines (in the KRITIS-DachG expressly within 24 hours – despite the deviating regulation "within business hours" in NIS2). The logic of impact also typically differs: NIS2 works more along the lines of facility types/sectors and size/relevance criteria, while the umbrella law works more along the lines of supply impact/threshold values (in practice, often along the 500,000 system).
What does this mean for affected companies?
For affected companies, this usually means a hybrid management system with shared evidence (e.g., ISMS for cyber/NIS2 plus BCM/resilience structures for physical and organizational resilience), combined with a noticeable increase in bureaucracy if evidence and processes are not consistently integrated.
The KRITIS-DachG results in particular in:
- Physical and organizational minimum requirements (e.g., emergency/crisis organization, property protection, action planning, exercises/reviews).
- Nationwide identification/registration and reporting requirements for significant incidents within the meaning of the umbrella law (typically physical/organizational; hybrid situations included).
- Increased responsibility and liability risks for management arising from organizational and compliance obligations.
- Residual risks from demarcation issues (e.g., in the case of cyber-physical attacks), dependencies on government situation assessments/risk assessments, and implementation details that have not yet been fully harmonized in the interaction between CER and NIS2.
In addition, there is an overlap with DIN/ISO 27001: An ISMS according to ISO/IEC 27001 is a very good organizational framework for cyber-related requirements (e.g., NIS2-related risk management and evidence management), but is not sufficient on its own for the physical resilience requirements of the KRITIS-DachG and should therefore be supplemented with resilience/BCM components (e.g., ISO 22301-oriented). Important: Certification can facilitate evidence management and increase maturity, but does not in itself protect against fines if specific obligations/evidence are not fulfilled vis-à-vis the authorities.
Conclusion:
The KRITIS umbrella law is intended to strengthen resilience, but in the short term it increases the pressure to implement and document, especially where NIS2 and physical resilience have to be organized "simultaneously."
If you are just starting the overall implementation, you are in the comfortable position of being able to take advantage of synergy effects, such as preparing for ISO 27001 certification. If you have already actively implemented NIS2 or even 27001, you will unfortunately face additional work and duplication.
Operators should now clarify the impact and program structure, because risk analysis, resilience planning, exercises, and reporting processes cannot be set up properly "in a few weeks."
Do you still have challenges to overcome in defining the detailed requirements? Do you need support with conceptual migration? Contact us!